If you have deployed ADFS 3.0 in your organisation you will find that by default only Internet Explorer works for SSO. To add support for Edge and Chrome we have to make some changes on the ADFS servers. By default ADFS 3.0 does not recognise the browser user agent for Chrome or Edge. So we need to add them to the ADFS config.
First of all we need to confirm that the browser headers are not present. Run the command.
Get-ADFSProperties | Select -ExpandProperty WIASupportedUserAgentsYou will now see a list of all browser user agents supported.
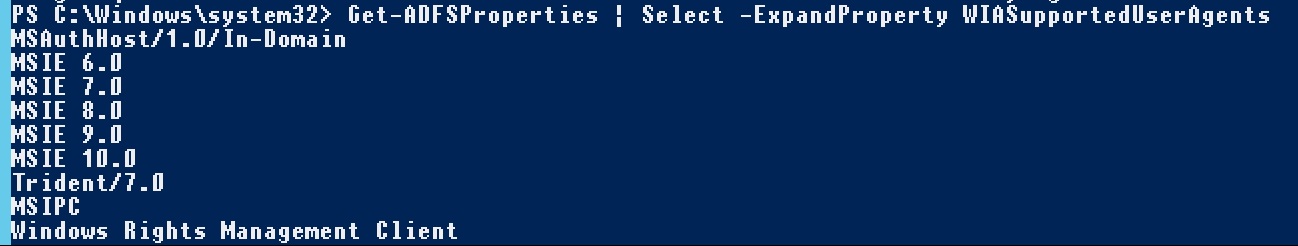
The ones we need to look out for are Edge and Mozilla 5.0. Unfortunately, you cannot just add the 2 needed. The command we need to run adds all the present ones and the new ones.
Set-AdfsProperties –WIASupportedUserAgents @("MSAuthHost/1.0/In-Domain","MSIE 6.0","MSIE 7.0","MSIE 8.0","MSIE 9.0","MSIE 10.0","Trident/7.0", "MSIPC","Windows Rights Management Client","Mozilla/5.0","Edge/12")Now we have them all present. They should all now be present. Run the Get-ADFSProperties command mentioned earlier to see the list.
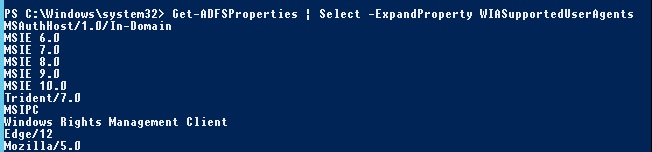
We can start restart the ADFS Services.
net stop adfssrvnet start adfssrvRemember to restart the service on every ADFS server.
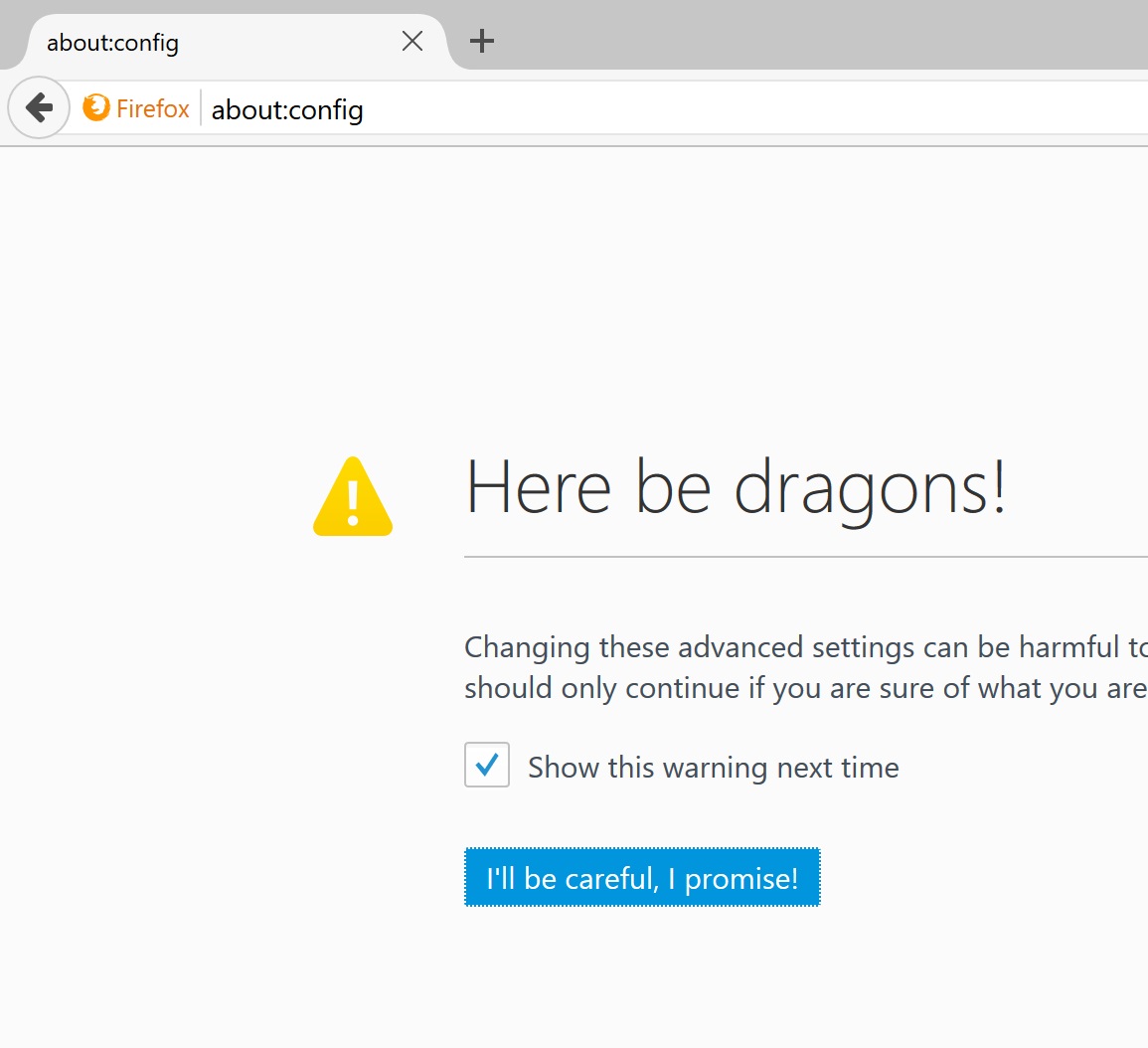
So far I haven’t been able to automate Firefox working across an organisation. On each machine you need to make a change in Firefox to allow it to pass through your network logon details to the ADFS page. Open a Firefox page and type “about:config” in the address bar. Then click on the “I’ll be careful, I promise!” button.
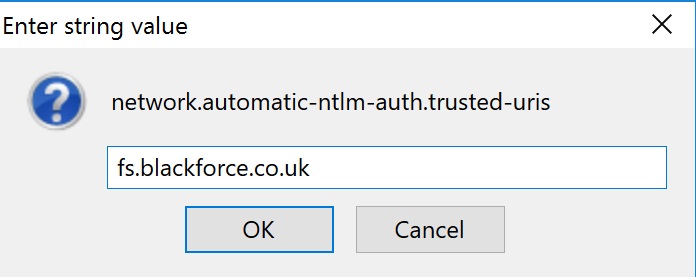
Search for network.automatic-ntlm-auth.trusted-uris in the search bar. Then double click on the line that appears.
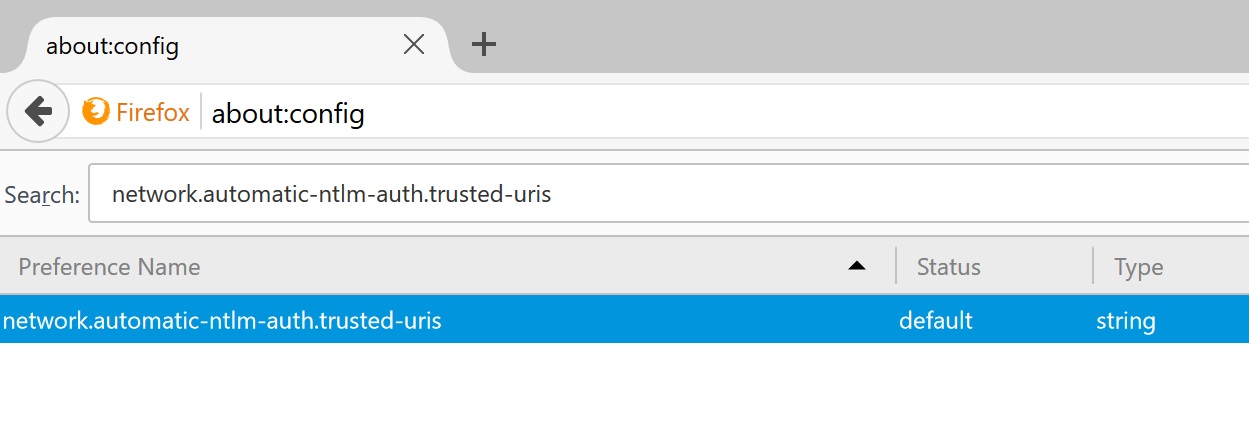
Add in the name of your ADFS URL. Do not add the https part. Once done click ok. Thats it all done 🙂
Update 03/05/18 :
Updated command to include all versions of firefox and edge
Set-AdfsProperties –WIASupportedUserAgents @("MSAuthHost/1.0/In-Domain","MSIE 6.0","MSIE 7.0","MSIE 8.0","MSIE 9.0","MSIE 10.0","Trident/7.0","MSIPC","Windows Rights Management Client","Edge","Chrome","Firefox")